Secure Online Network 624591013 for Growth
A Secure Online Network 624591013 for Growth enables scalable collaboration while tightening governance and risk posture. It emphasizes trusted authentication, least-privilege access, and auditable rights to curb data exposure. The approach pairs phishing resilience with proactive incident planning and continuous monitoring to sustain performance under expansion. Yet, decisions around segmentation and governance will determine resilience in practice, shaping whether growth proceeds with confidence or reveals gaps. The next move could redefine the risk profile and competitive edge.
What a Secure Online Network Delivers for Growth
A secure online network delivers measurable growth by enabling trusted, scalable collaboration and faster decision cycles while mitigating cyber risk. It emphasizes network governance, phishing resilience, and user analytics, incident response planning, and network segmentation, data minimization, and access reviews. This strategic, risk-focused, proactive framework empowers freedom-seeking teams with targeted controls, proactive monitoring, and disciplined improvements for sustained competitive advantage.
Build Trust: Authentication, Access, and Identity Best Practices
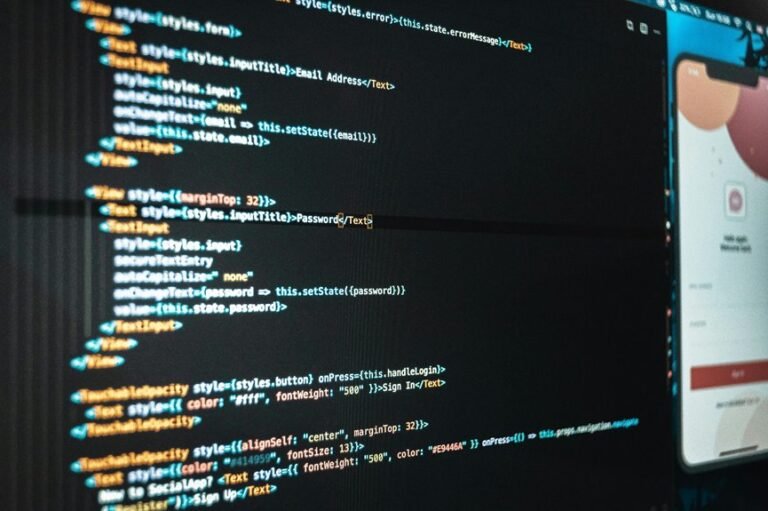
How can an organization establish trust from the outset? The approach emphasizes authentication governance and identity federation as core controls. It prioritizes risk-aware access design, minimizing friction while enforcing least privilege, continuous verification, and auditable rights. Proactive governance aligns stakeholders, curbs shadow access, and strengthens enrollment, provisioning, and revocation processes. This builds reliable, freedom-supporting trust across ecosystems.
Defend and Optimize: Threat Mitigation and Performance Resilience
Strategic risk management enables resilient operations, ensuring freedom to innovate with confidence in robust, auditable protective measures.
Privacy-By-Design: Designing Scalable, User-Friendly Security for Expansion
Privacy-By-Design emerges as a proactive framework for scalable, user-friendly security during expansion, prioritizing data minimization, consent clarity, and transparent governance.
The approach translates privacy by design principles into concrete controls, aligning risk assessment with rapid deployment.
It emphasizes modular, scalable security architectures, governance transparency, and user empowerment, fostering freedom while reducing risk from pervasive data growth and evolving threat landscapes.
Conclusion
In pursuit of growth, the Secure Online Network 624591013 hinges on proactive governance, auditable rights, and least-privilege access. The framework strengthens phishing resilience, user analytics, and incident response while enforcing data minimization and robust segmentation. By balancing protection with scalable collaboration, it turns risk into strategic advantage. Like a well-tuned orchestra, the system harmonizes authentication, access, and governance to deliver resilient performance and sustainable innovation, guiding expansion with disciplined vigilance.